Let’s not beat about the bush: We’re living through some very unusual times. As I write to you, from a government-imposed State of Emergency to deal with the fallout from COVID-19, I can’t help but be thankful for the technologies in place that have allowed me to keep working, to stay in touch with colleagues and loved ones, and to assist other organisations with rapidly enabling their own remote working capabilities – all from the relative safety of my own home.
Since the inception of my organisation in 2013, we have always been “remote ready”: we were born in the cloud, and even before Teams came along, we were using technologies like SharePoint Online, OneDrive and Skype for Business to deliver remote working capabilities. Microsoft Teams is simply the latest iteration of this, bringing both communication and collaboration workloads into the one client experience, as well as making it easier than ever to extend on “out-of-the-box” capabilities deploying custom Teams apps and Bots to solve business issues. And whilst many organisations have been on their own individual journeys to Modern Ways of Working, if there’s one thing COVID-19 has achieved it has expedited these plans: legitimising the very reason organisations should be deploying these technologies in the first place.
One component of the Microsoft Teams platform that’s been getting a huge increase in usage of late is of course Online Meetings. As you would imagine, online meetings have been part of a typical “day in the life of” for me for some time, but now: it’s different. Online meetings have become my primary means of communication with clients, colleagues, and even family and friends (weekend Jackbox Games sessions via Teams are fantastic!)
Given the sudden surge in popularity of all types of online meeting platforms, what better time to review Microsoft Teams security: How does Microsoft protect me and my data?
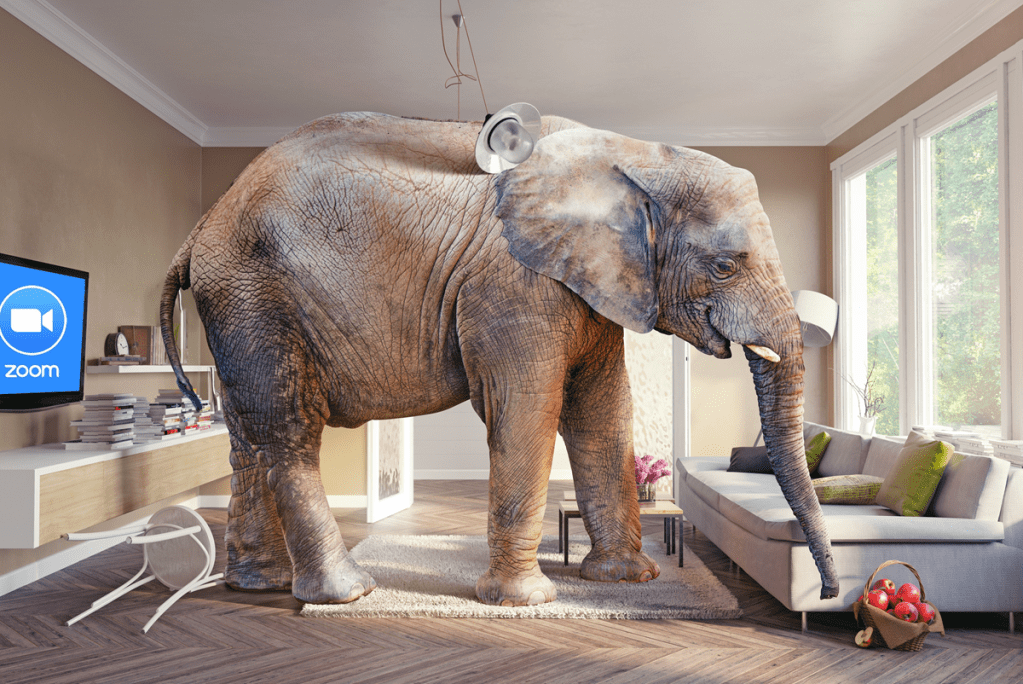
The Elephant in the Room
Before I go through the various security features Microsoft Teams offers, I should of course address the very reason I decided to put this blog together in the first place. Microsoft Teams hasn’t been the only online meeting platform to see huge increases in usage over the last few weeks: Cisco’s WebEx, Google’s Hangouts Meet and Zoom have also seen huge increase in activity. Of these providers, it’s been the latter that has not only seen a huge increase in usage, but has also drawn a huge amount of criticism.
And for good reason.

There have been a number of security issues uncovered with Zoom over the last few months, continuing a trend that started well before the current COVID-19 crisis. Back in July 2019 we saw a serious zero-day vulnerability uncovered where Zoom were installing a local web server on Macs. Why? To remove clicks from the meeting join experience. In an interview with The Verge, Zoom’s Chief Information Security Officer Richard Farley said that:
“Ultimately, it’s based on the feedback of the people that have been following this and contributing to the discussion. Our original position was that installing this [web server] process in order to enable users to join the meeting without having to do these extra clicks — we believe that was the right decision. And it was [at] the request of some of our customers.
But we also recognise and respect the view of others that say they don’t want to have an extra process installed on their local machine. So that’s why we made the decision to remove that component — despite the fact that it’s going to require an extra click from Safari”
RICHARD FARLEY – CISO, ZOOM
Since then, there have been numerous other security issues uncovered (a timeline of which can be found here). At time of writing, I’m learning of yet another: A security researcher found a way to access and download Zoom recordings – even after they had been deleted.
As expected, Zoom’s security woes have resulted in various government bodies (US Senate, Australian Government, Australian Defence Force), private organisations (SpaceX, NASA) and educational institutions (Singapore, New York City Department of Education) banning the use of Zoom for meetings. For security vulnerabilities identified to date (well, not including the most recent but all the others), Zoom’s CEO Eric Yuan has come out and apologised. Zoom is now committing to undertake a 90-day freeze on feature development in order to prioritise resolving these security issues. It does beg the question: is security not considered the most paramount deliverable when deploying any new feature or capability? Should feature delivery be at the expense of security, compliance and privacy?
It was at this point in the article that I was going to provide a (probably quite boring) list of each and every feature that Microsoft employs to ensure your security and privacy are protected when using Microsoft Teams. Rather than reinvent the wheel, you can find links to detailed information Microsoft provides in the Useful Links section at the end of the article. Instead, let’s start with some of the security issues Zoom has encountered, and work back through specific configuration and default behaviour that protects your security and privacy when using Microsoft Teams.
Zoom Offers New Privacy Option for Paid Accounts
Ok, so not a security issue per se, but one I think deserves a mention. In this blog post, Zoom said that, starting April 18th:
“Every paid Zoom customer can opt in or out of a specific data centre region. This will determine the meeting servers and Zoom connectors that can be used to connect to Zoom meetings or webinars you are hosting and ensure the best-quality service”
BRENDAN ITTELSON – CTO, ZOOM
The driver for this was of course the discovery that Zoom call traffic (specifically, transmission of encryption keys) had been routed via servers located in China, even though not a single meeting participant was actually in China. Given that it’s well within the rights of the Chinese government to legally request and obtain encryption keys for secure traffic that traverses their region, this is less than ideal.
What about Teams?
Whilst Office 365 does exist in China, it’s not operated by Microsoft: it’s operated by 21Vianet. Microsoft license their service and technology to 21Vianet, who only provide a subset of Office 365 capabilities, of which Microsoft Teams is not one of them:
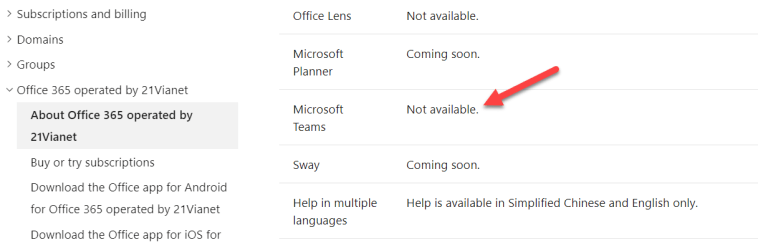
So, unsurprisingly, Microsoft does not route any traffic (Teams or otherwise) via China. Moving on.
Zoom “rolls their own” encryption scheme
Leading on from the previous issue above, the same researchers that discovered Zoom call encryption keys traversed China also discovered that the encryption keys themselves were not up to industry standards. Zoom’s own security documentation claims that they can use “AES-256” encryption for meetings, although the use of the term can does not necessarily mean does. On further investigation, the researchers also found that:
“In each Zoom meeting, a single AES-128 key is used in ECB mode by all participants to encrypt and decrypt audio and video. The use of ECB mode is not recommended because patterns present in the plaintext are preserved during encryption”
BILL MARCZAK & JOHN SCOTT-RAILTON – MOVE FAST & ROLL YOUR OWN CRYPTO, APRIL 2020
So in summary, not only were encryption keys traversing a region where they may be subject to compromise, the keys themselves weren’t all that secure in the first place.
What about Teams?
All network communications in Teams are encrypted by default. No need to enable, it’s by design. All Teams services use a combination of Public Key Infrastructure (PKI) certificates and various industry-standard encryption techniques (OAUTH, TLS), and uses Secure Real-Time Transport Protocol (SRTP) to secure media streams (audio, video and content sharing). This includes the use of 256-bit Advanced Encryption Standard (AES) encryption. Check out this Microsoft Docs article for more details.
Zoombombing
If you’re not familiar with the term, “Zoombombing” refers to the practice of uninvited attendees joining a Zoom meeting, who may then decide to go forth and do things like share pornographic images with participants. Given the huge uptake of Zoom by not just businesses but also by educational institutions, this is far from ideal.
How does Teams Prevent this?
First and foremost, Teams provides the ability to disable “anonymous” meeting join for an entire Office 365 Tenant. This is configured from the Teams Admin portal under Meeting Settings:

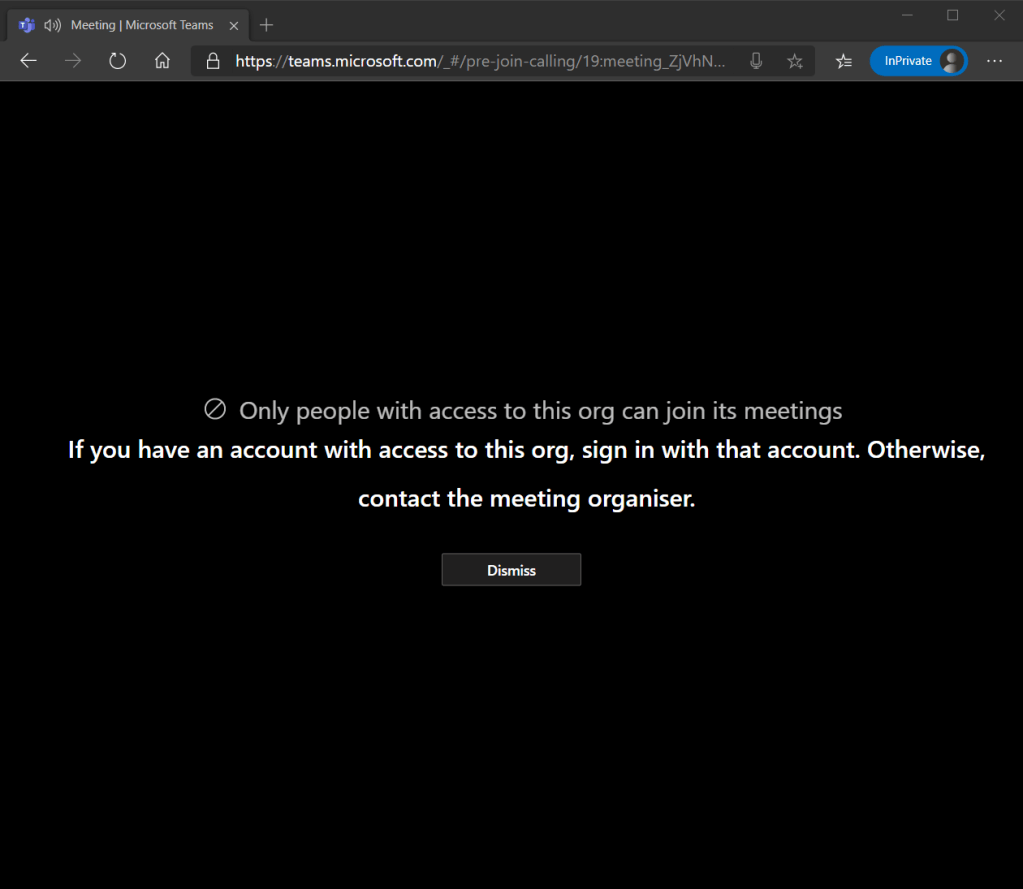
If I disable this, with a single setting I can ensure any meeting participant that wants to join meetings within my organisation must be an authenticated user. This means they need to be signed in with a valid active directory account. If a rogue user did somehow manage to get access to the meeting join link (say, a student copied it to a public forum or gave it to friends), and attempted to join as an unauthenticated user, meting entry will be denied:

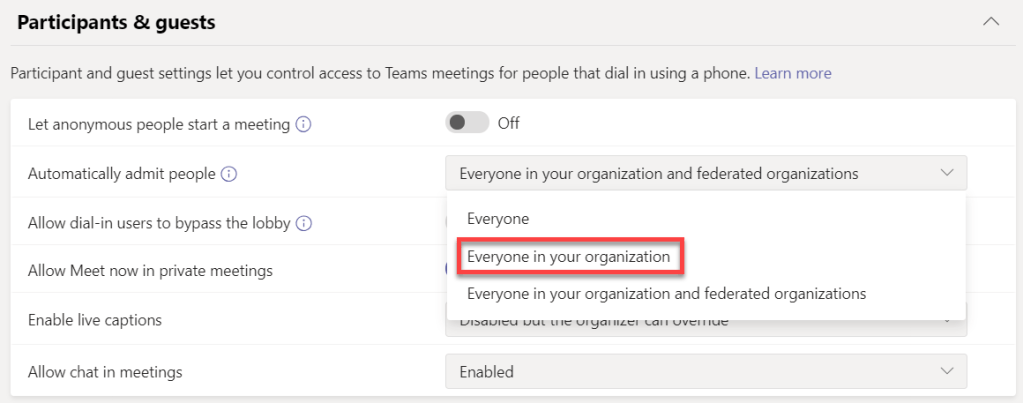
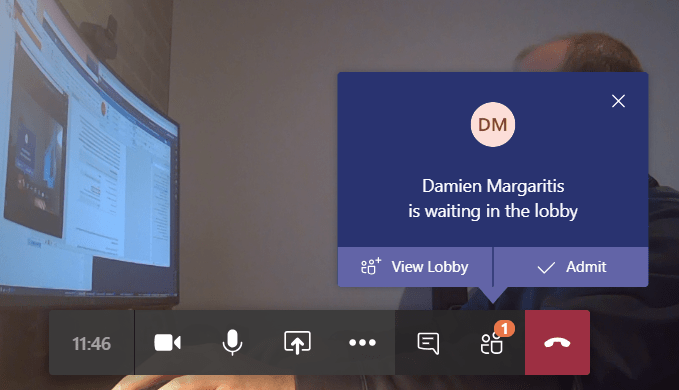
Now, disabling anonymous meeting join does not mean that no external participants can join your meetings, it just means that anonymous (unauthenticated) external participants cannot join your Teams meetings: externals can still join as long as they are authenticated against their own Office 365 Tenant. If you don’t want external authenticated meeting participants to automatically be admitted to your Teams meetings, you can configure the Teams Meeting Policy (more in this below) to limit automatic entry to Everyone in your organisation, rather than Everyone in your organisation and federated organisations. This will force them to the lobby to be admitted by the meeting organiser:
The Teams Meeting Policy
The Teams Meeting policy is used to control what meeting features are available to meeting participants for meetings that are scheduled by users in your organisation. The below screen grab shows what the default configuration looks like, which applies to all Teams users out of the box. You can of course create as many meeting policies as you like, allowing you to centrally control which users can do what:

Looking at the Participants and guests section above, and assuming that I’ve allowed anonymous meeting join for my organisation, I have granular control over how anonymous meeting participants join my meetings. Default settings do not allow anonymous participants to start a meeting, they are not automatically admitted to the meeting (must go via the meeting lobby), and dial-in (PSTN) participants must also wait in the lobby until admitted by a meeting organiser\presenter.
A Little bit on Meeting IDs
As a side note, a contributing factor to Zoombombing being able to occur in the first place has been the relative ease “Zoombombers” have been able to access a valid Zoom meeting ID. Meeting IDs were easily accessible (displayed in plain text) in the app’s title bar (since removed from Linux, Mac & Windows apps), and default password settings (no meeting password) also meant that Zoom permitted anyone to join a meeting as long as they had the Meeting ID, no password authentication required. Couple this with “War Dialers” – automated tools capable of finding valid Zoom meeting IDs and which ones are not password protected – and you can see why this might be an issue.

To be fair, Zoom are working to address these issues, and I understand what they were trying to do in the first place: make it super easy to join a Zoom meeting. Unfortunately, designing for this level of simplicity and not enforcing some sort of authentication mechanism by default has been a major contributing factor to Zoom’s security woes.
What about Teams?
To start with, there’s no concept of a personal, static Meeting ID within Teams meetings. Each meeting (ad-hoc or scheduled) has a unique meeting identifier, one that’s much more complex than a 9-11 digit number, and it’s never on display during a Teams Meeting. Here’s an example of a Teams meeting URL (before you try and join, I’ve changed two characters 😊):
https://teams.microsoft.com/l/meetup-join/19%3ameeting_ZDg5YWY0ZDgtNmNiNi00NTMwLTg4OWctNzBlM2U5OABkNzNl%40thread.v2/0?context=%7b%22Tid%32%3a%22466808bd-711d-4429-8642-582b60269a29%22%2c%22Oid%22%3a%22d832bd6a-8fba-4ca7-b866-408574a2029e%22%7d
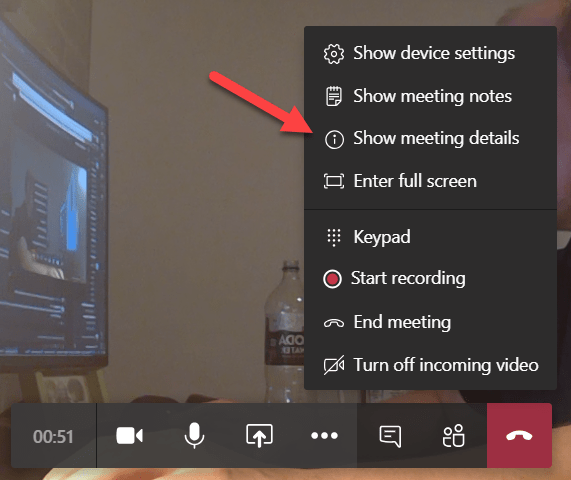
If you are in a meeting and you want to share meeting join information “manually”, Teams supports this by allowing you to copy all meeting join information to the clipboard and pasting into a medium of your choice:

500,000 Zoom accounts sold on hacker forums
As reported by Bleeping Computer, thousands of leaked Zoom account details have been appearing on hacker forums. Details being traded include a victim’s email address, password, personal meeting URL, and their Host Key (a 6-digit PIN used to claim host controls in a Zoom meeting).
Now, it should be noted that Zoom itself need not be hacked in order for these lists of compromised accounts to exist. Humans have a propensity to use the same password for multiple online services, so it only takes another service where you’ve used the same password to be compromised for a hacker to try their luck using your creds somewhere else – say Zoom for example.
Unsure if any of your passwords been compromised? Go and find out at HaveIBeenPawned?
How does Teams ensure this doesn’t occur?
Given that Teams is built on top of Office 365, Azure and other related Microsoft cloud technologies, it’s no surprise that authentication is handled by Azure Active Directory (Azure AD\AAD). Azure AD is Microsoft’s cloud-based enterprise identity service, and it provides things like Multi-Factor Authentication and Conditional Access to help protect your users from cybersecurity attacks. These security capabilities aren’t unique to Microsoft Teams: Azure AD underpins authentication across Microsoft’s entire ecosystem. I don’t use different credentials to access Teams than I do with any other Microsoft platform, including my Windows 10 PC. Couple that with Single Sign On (SSO), and I now have one set of secure credentials that I use to access my Microsoft devices and any subsequent applications I open without needing to enter in credentials over and over again (to be honest, I don’t use a password at all – I use Windows Hello).
Of course, given that we’re using one set of creds to access all our cloud services (including Teams), how does Microsoft protect me if my username and password are somehow compromised?
Multi-factor Authentication
If you don’t use Azure AD Multi-Factor Authentication (MFA) today, stop reading and get onto it. Right now. There is literally no easier way to protect against 99.9% of cybersecurity attacks. Deploying MFA ensures that access to you account is only possible if you have both the account password and access to a secondary device (sometimes referred to as “something you know, something you have”) that provides an additional layer of security. The concept isn’t new, it’s just a little more advanced than it used to be – who remembers these?

Today, we typically use an app on a smart phone to support MFA, and I don’t have to enter a code anymore, I can simply click approve:

To get the above screen shots, I actually had to “downgrade” MFA capabilities on my account, because today I’ve gone one step further and don’t use a password at all when I need to sign-in to Office 365, I use Passwordless MFA – check out more on that here.
Conditional Access
So, my account credentials are protected using MFA. What if I want to go even further?
Conditional Access is a feature of Azure AD that enables organisations to define specific conditions for how users authenticate and gain access to applications and services. For example, I can use a user’s location (in the office or remote? In Australia? Or Overseas?), the device they’re trying to use (is this a device registered against our organisation or not?), the application and even input from real-time risk analytics to decide whether to allow someone access to Teams:

Here’s an article from 2017 (yes, it’s been possible to do stuff like this for ages) that talks about using Conditional Access with Microsoft Teams.
Conclusions
I think it’s safe to say that the last few months have seen unprecedented change in how people around the world work, communicate, and stay productive. The trend to support “remote ways of working” is nothing new, but what is new is organisations moving to using these tools so rapidly in response to a global pandemic. Human nature is to gravitate towards a solution that provides the path of least resistance: it’s something we refer to in the IT world as “Shadow IT”. If you don’t give your users tools to help them be productive, they will find a way, and we’ve seen this occur on a mammoth scale with the uptake of Zoom to meet online meeting needs. Unfortunately, it’s come at a cost to security and privacy. You don’t have to take my word for it: when Zoom’s CEO Eric Yuan was asked if he would now prioritise security in the wake of all these security issues:
“If you asked me this question one year ago, I would hesitate to say yes. But now, absolutely yes. We’re going to transform our business to a privacy-and-security-first mentality.”
ERIC YUAN – CEO, ZOOM
For any new feature or capability being rolled out to Microsoft Teams, security and compliance are absolute fundamentals. Microsoft have a commitment to ensuring privacy and security for its customers before all others – there business and reputation depend on it. Jared Spataro, Corporate Vice President for Microsoft 365 captures this commitment perfectly:
“Now more than ever, people need to know that their virtual conversations are private and secure. At Microsoft, privacy and security are never an afterthought. It’s our commitment to you—not only during this challenging time, but always. Here’s how we’re working to earn your trust every day with Microsoft Teams”
JARED SPATARO – CORPORATE VP, MICROSOFT 365
For Zoom, a core focus on features and simplicity has come at the expense of security and privacy. If these things are important to you and your organisation, use Microsoft Teams.
Useful Links
Check out the following links for more on Microsoft Teams security and Meeting Policy configuration:
Microsoft Compliance Certifications
Privacy and security in Microsoft Teams
Microsoft 365 Security Documentation
Microsoft Teams Security Guide
Top 12 Tasks for Security Teams to Support Working from Home
Leave a comment